Horizon Report
The state of cybersecurity in healthcare

Many Americans knew of cybersecurity breaches prior to this year, but the large-scale impact of the Equifax breach of 2017 put them on the map for most of us. From dinner table to conference table, the breach started numerous conversations about protecting personal information. In turn, it caused many organizations to re-evaluate their cybersecurity program. Just as the Enron scandal of the early 2000s triggered a change in accounting standards, experts predict that, over time, this breach will have a significant impact on regulation. The attention the Equifax breach generated will no doubt impact how patients (consumers of healthcare) view organizations that have been hacked. One report suggests that over 40 percent1 of consumers would abandon or hesitate to use a health organization if it had been hacked. Even if that number were 5 or 10 percent, many healthcare organizations could not survive the financial ramifications associated with declining patient volume.
Unfortunately, healthcare leaders are stuck in the crosshairs of consumers and hackers. While consumers require transparency, access to information and assurance that their personal health information will remain safe, hackers are busy compromising patient information at a faster speed than ever before. As healthcare IT organizations strive to become more accessible and “open” to support patient engagement initiatives, hackers continue to target and exploit healthcare organizations for monetary gain. The required investment in cybersecurity is often overlooked or under- funded until an incident occurs. At that point, the damage to your organization’s reputation may have already occurred.
Healthcare organizations must strike a balance between enabling patient engagement initiatives and securing patient data. While there is no simple fix to this complex challenge, healthcare organizations often focus on the wrong areas at the wrong time. Organizations must develop and execute the fundamentals of security first before exploring advanced solutions. This requires a defensive, in-depth approach to cybersecurity that is grounded in a detailed HIPAA Security Risk Analysis and a companion corrective action plan.
As healthcare leaders, we must evaluate and manage cybersecurity risks like any other risk and be proactive in protecting our organization. Managing cyber risk is complicated and, to be successful, your entire organization must be engaged.
My hope is that the Horizon Report builds awareness about threats and provides you valuable insight. We welcome your feedback and perspectives at horizonreport@fortifiedhealthsecurity.com. Enjoy.
Regards,
Dan L. Dodson
1 Source: Top health industry issues of 2016: Thriving in the New Health Economy, PwC Health Research Institute
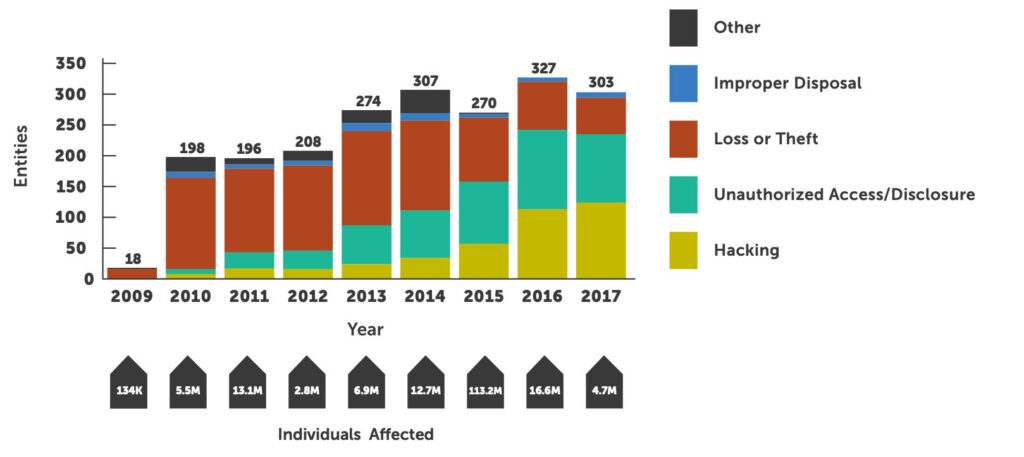
The state of cybersecurity and the frequency of breaches in the healthcare industry intensified in 2017. The number of people directly impacted by a breach decreased year-over-year, but the number of entities impacted increased 25 percent over the last 12 months2. This validates the fear of many healthcare organizations: hackers have momentum and breaches are happening more often than ever before. Our adversaries are focused on obtaining valuable health information. In most cases, these breaches are deliberate and directly aimed at obtaining sensitive information for monetary gain. As of mid-November 2017, a total of 303 healthcare entities had experienced a large breach this year. This is on pace to surpass the 327 breaches experienced in 2016. So far this year, over 4.7 million health records have been compromised.
According to data provided by The Office for Civil Rights (OCR), hacking continues to be the biggest cause of breaches for the sixth year in a row. This year, over 40 percent of all breaches were caused by hacking — a 10 percent increase in the number of entities impacted by hacking in 2016. Every year since 2012, when hacking represented only 8 percent of all breaches, it has been a larger cause of breaches than the prior year.
According to the U.S. Department of Health and Human Services Office for Civil Rights (OCR), this has been the case since 2009. The OCR Wall of Shame also found that in the first week of 2018, there were four major breaches containing more than 500 patient records. This is the same number of breaches reported in the first week of 2017, but the momentum has increased from there. Through the first five months of 2018, there have been 149 breaches reported with over 2.8 million patients impacted, as compared to 134 breaches impacting 2.0 million patients during the same period in 2017. This represents an 11% increase in the number of entities affected and a 35% increase in the number of individuals affected.

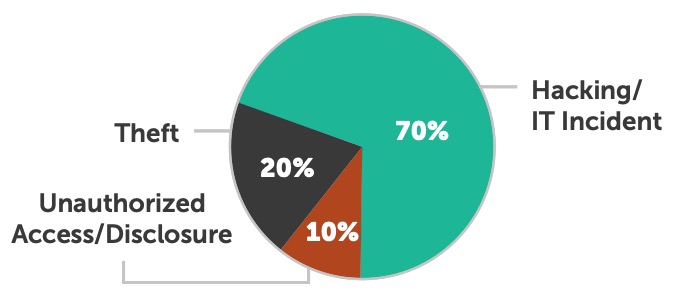
This data confirms that hacking not only makes up a larger percentage of all breaches, but the number of entities breached by a hack has also increased significantly since 2012. Hacking has also affected the largest number of people thus far in 2017.
This breach data underscores the importance of a solid security program focused on the fundamentals of patching and employee education. Having a well-executed security program can significantly decrease the chance of a large-scale breach.
Providers continue to be the most targeted and breached type of healthcare organization in 2017. This has been the case since OCR began collecting breach data in 2009. Providers accounted for 80 percent of all entities breached thus far in 2017 and over 90 percent of all individuals impacted. This is more than health plans and business associates combined. Providers have experienced over 240 breaches this year; we expect that number to climb to over 260 by end of year.
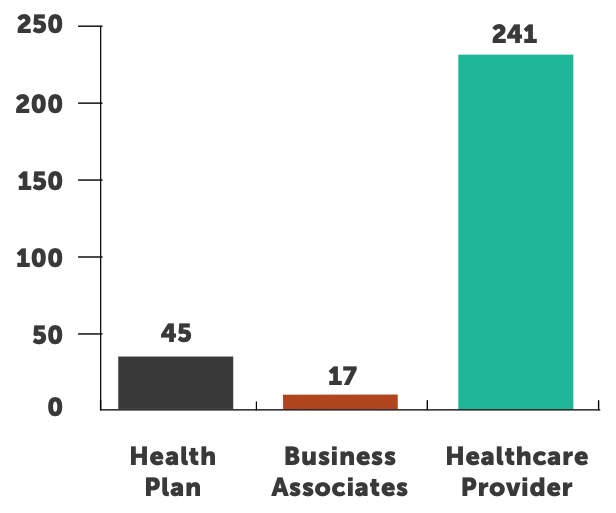
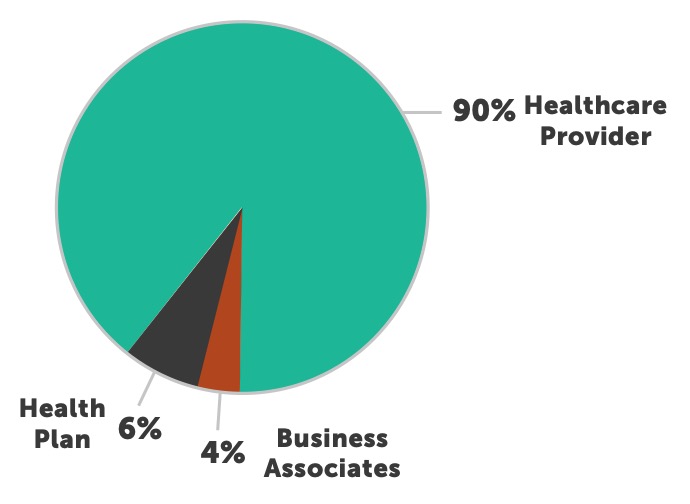
Unlike 2016, there was no single breach in 2017 that impacted over one million individuals. The total of the top five breaches affected over two million people and represented over 43 percent of all those impacted by a breach. Providers accounted for 18 of the 20 largest breaches thus far this year and hacking was the cause of 17 of those 20 breaches. This further emphasizes the focus our adversaries have on the provider segment of healthcare and highlights hacking as their weapon of choice.

We found that large budgetary purchases or complex software implementations don’t always pose a challenge. Instead, the fundamentals of security and risk management are usually missing. Policy and procedures have always been at the heart of a strong security and risk management program. They set the foundation for the organization’s rules, guidelines, standards and expectations. Typically, we see organizations fall into one of three groups:
GROUP ONE: No policy or procedures are approved and published. This is more common with business associates or newly merged health systems that haven’t decided whose policy sets will be the system’s adopted set.
GROUP TWO: Organizations with approved and published policy sets that aren’t being followed. This is particularly dangerous, as senior leaders assume the organization is following the “rules” — yet when you get to the “ground level” it is quite the opposite. Senior leaders possess an unwarranted level of comfort and make decisions on priorities and resources without a clear picture of the organization and its risk.
GROUP THREE: Organizations that haven’t reviewed and/or updated their policy sets in a number of years. This activity is critical since technology, network environments, leadership, and federal, state and local regulations are always in flux. A sound risk management program will account for all of these types of changes and ensure the policy/procedures reflect those changes.
Regardless of where organizations fall into these groups, having effective policy and procedures should be step one in developing and managing security and risk.
The lack of critical asset inventories is another foundational challenge for many healthcare organizations. This year, Fortified has assisted a number of organizations that were being investigated and/or audited by OCR. Throughout that process, organizations have struggled to answer a common question from OCR: “Where is your asset inventory? Specifically, where is the inventory of devices that store, process or transmit ePHI?” Not surprisingly, OCR has a deliberate reason for asking this question. How can you protect ePHI if you don’t know where it is? Understanding where your sensitive information resides will help you tailor your controls and safeguards to that specific environment. This type of focused effort can help save time and budgets from being overtaxed.
Organizations must commit themselves to vulnerability management. It is mission-critical to address the real gaps in security that leave sensitive information exposed. In our Mid-Year Horizon Report, we wrote about utilizing a defense strategy around people, process and technology. While each holds its own challenges, in the past 12 months Fortified has seen a number of examples of poor processes, specifically with regard to vulnerability management (Wannacry, Petya, Equifax, etc) that have caused the most issues. There is a seemingly endless onslaught of patches, security updates and fixes to operating systems, applications, databases and networking devices.
While healthcare is concerned with EHR transitions or upgrades, movements to the cloud, or any other IT project, it is imperative that a priority be set on getting back to the fundamentals of risk management and good cybersecurity hygiene. This begins with regular Security Risk Analyses. We must commit ourselves to vulnerability threat management if we want and expect to improve our security posture.
100%
of web application penetration tests result in demonstrating the ability to access ePHI
97%
93%
13%
10%
68%
72%
25%
54%
33%
29%
72%
25%

FIRST, healthcare entities are still not understanding the need for strong security engineering when constructing and deploying hardware and software solutions.
SECOND, basic security functions such as strong passwords, password management and patching are being forgotten or totally ignored.
THIRD, access to PHI is not being configured with “need to know” or least privilege permissions
3 This section contains contributions from James Gallagher, Security Analyst at Fortified Health Security.
A Look at Fortified’s 2017 Predictions
Double-Digit Increases in Breach Activity: As hackers become more advanced and better equipped, healthcare organizations will experience a 10-15 percent increase in the number of cybersecurity breaches in 2017.
So how did we do? A review of OCR Breach Notification data shows the healthcare industry has seen a 15.6 percent increase in breaches: from 208 in January-October 2016 to 248 for the same time period this year. A 12-month comparison of November 2015-October 2016 to November 2016-October 2017, reveals an even more damaging 24.8 percent increase. As malicious actors continue to assault healthcare organizations, we remain diligent and steadfast in our agenda to improve the security posture of healthcare.

Boards Will Keep Their Heads in the Sand and Hope for the Best: Some healthcare organization boards have already begun managing cybersecurity risk in the same manner as other business risks. Unfortunately, they often become engaged in cybersecurity risk management after a significant event. Many boards remain content to retain a reactive posture in dealing with cybersecurity concerns. The results will be costly.
So how did we do? The double digit increase in breaches bolsters our prediction that boards will remain reactive. We still find CISOs and other security leaders struggling to gain board-level support for the necessary senior management focus and resources required to properly manage and remediate cybersecurity risk. Fortified hasn’t changed our perspective or priorities in combatting this very real problem.
OCR Moves Towards a National Framework for Healthcare: The Office for Civil Rights will take steps to develop a national framework that is prescriptive in its requirements to guide Covered Entities and Business Associates to the desired end result with regard to protecting sensitive data and ePHI. OCR will finally adopt the HITRUST Alliance’s Common Security Framework (CSF) as the national standard or work directly with the National Institute of Standards and Technology (NIST) in developing a new framework that meets the unique needs of the healthcare industry.
In September 2017, consumer credit reporting agency Equifax experienced a data breach that compromised the personal information of approximately 143 million US consumers (roughly half of the US population). The compromised data included numerous types of personally identifiable information (or PII) including name, birth date, address, credit card number, social security number and driver’s license number.
Hackers exploited an unpatched vulnerability in ‘Apache Struts’, a web application framework in use by Equifax, to ultimately gain access to the now-compromised data.

1
2
3
To a malicious actor, the value of stolen data is significantly reduced or eliminated when encryption techniques are applied to data at rest.
4
Failure to create and implement such a plan can result in loss of consumer confidence, consumer trust, decreased revenue and compliance violations.
Like previous high profile breaches, the Equifax breach is an educational opportunity for all healthcare organizations. Analyzing and understanding how it happened, the internal incident response actions, and most importantly, how clients respond to this breach can help healthcare organizations avoid or be better prepared for a future breach.
3 This section contains contributions from James Gallagher, Security Analyst at Fortified Health Security.
*Sources:
Michael Hiltzik – http://beta.latimes.com/business/hiltzik/la-fi-hiltzik-equifax-breach-20170908-story.html
Lily Hay Newman – https://www.wired.com/story/how-to-protect-yourself-from-that-massive-equifax-breach/
Panoptex Technologies – http://panoptex.com/equifax-data-breach-stopped/
Anne Burroughs – https://www.trueprocess.com/equifax-breach-means-healthcare-organizations/
1
2
3
4

Security can no longer be referred to as an IT problem. The consequences of bad security now reach into every aspect of business. Thus, security should be treated as a business issue and dealt with accordingly. Ensure that sound security decisions are being included at every level of the business.

Institute a patch management program – Patch your systems. Then patch again. And again. It is a monotonous, somewhat challenging cycle but is extremely important. Much of the malware today is predicated on the vulnerabilities that patching will fix. Establish a patch management program and ensure it is operating properly and often.

Corrective Action Plans are designed to help remediate issues within your business. They are also designed to have a finite shelf life. Ensure any Corrective Action Plans you have are actively being worked and have a completion date firmly established. Remediate quickly to avoid a costly breach.

Healthcare entities are required by law to adhere to HIPAA. But are they truly compliant? Breaches due to HIPAA compliance negligence can result in legal action and hefty fines. Confirm that your organization can clearly demonstrate compliance to HIPAA regulations by having a HIPAA risk analysis performed annually. Ensure any and all Corrective Action Plans resulting from the assessment are fixed in a timely manner.

Chief Executive Officer
Dan L. Dodson serves as CEO of Fortified Health Security, a recognized leader in cybersecurity that is 100% focused on serving the healthcare market. Through Dan’s leadership, Fortified partners with healthcare organizations to effectively develop the best path forward for their security program based on their unique needs and challenges. Previously, Dan served as Executive Vice President for Santa Rosa Consulting, a healthcare-focused IT consulting firm, where he led various business units including sales for the organization. He also served as Global Healthcare Strategy Lead for Dell Services (formally Perot Systems), where he was responsible for strategy, business planning and M&A initiatives for the company’s healthcare services business unit. Dan also held positions within other healthcare and insurance organizations including Covenant Health System, The Parker Group and Hooper Holmes. Dan is a thought leader in healthcare cybersecurity and is a featured media source on a variety of topics including security best practices, data privacy strategies, as well as risk management, mitigation and certification. He was elected to the Association for Executives in Healthcare Information Security (AEHIS) Board of Trustees in 2022. In 2018, Dan was recognized as a rising healthcare leader under 40 by Becker’s Hospital Review and regularly speaks at industry-leading events and conferences including CHIME, HIMSS and HIT Summits. He served on the Southern Methodist University Cyber Security Advisory Board. Dan earned an M.B.A. in Health Organization Management and a B.S. in Accounting and Finance from Texas Tech University.

Vice President
Ryan focuses on increasing client security posture through driving collaboration between sales and operations teams. Prior to joining Fortified, he served as the Deputy Chief Information Officer for the New York State Division of Military and Naval Affairs and as a Director of a security and privacy healthcare IT consulting practice, in addition to working in the information security office for organizations such as MetLife and Memorial Sloan-Kettering Cancer Center. He holds an M.B.A. from Norwich University, as well as Certified Information Systems Security Professional (CISSP) certification and is a HITRUST Common Security Framework (CSF) certified practitioner.

Director of Services