Ever clicked on a website link that you shouldn’t have? We’ve all made that mistake at least once, and chances are nothing bad happened. But the stakes are considerably higher in a hospital environment. Patient care takes place 24/7/365, and any cyberattack can cripple the ability to treat patients.
More than 90% of cyberattacks start with phishing — and the numbers keep rising. In 2022, phishing attacks increased 87% across industries, while advanced phishing attacks surged 356%.
Why? Because as hospitals have focused spending on increasing their technical controls, cybercriminals have pivoted to the low hanging fruit: humans.
One of the most valuable things security teams can do to protect their hospital and patients is prioritize securing the human layer. Here are some effective ways to do that within your healthcare organization.
Balance compassion with cyber caution
Healthcare workers are, at their core, compassionate individuals. This altruistic spirit is not just a byproduct of the profession, it’s often the primary reason many are drawn to healthcare, viewing it more as a calling than merely a job.
However, this innate drive to help can sometimes inadvertently lead to vulnerabilities. Phishing, for example, is a persistent threat that capitalizes on this trust and benevolence. And in the bustling environment of healthcare, it’s not uncommon for someone to hastily click on a link or open an email attachment without contemplating potential risks.
Communications, whether they’re emails, texts, or phone calls that appear to be from trusted colleagues or superiors, can be fabricated. The hacker’s goal may not even be to compromise the healthcare system, but instead secure an easy payday by cracking a password that gives them access to someone’s bank account.
These potential pitfalls underscore the importance of robust cybersecurity awareness training for hospital employees. Yet, several challenges persist in implementing effective training:
- Counterbalancing the innate trusting nature of healthcare professionals
- Cutting through the daily chaos and demands of hospital life
- Navigating increased training mandates or union-imposed training restrictions
It’s possible to harmonize a culture of genuine care with one of cyber vigilance. The key is consistent, meaningful training, reinforced with practical tests like phishing exercises.
Educate and engage your leadership
To cultivate a robust cybersecurity culture and minimize human risk, it’s essential for your hospital’s C-suite to fully support and invest in cybersecurity training initiatives and technologies.
While your hospital leadership, including the Board of Directors, are undoubtedly cognizant of the escalating cybersecurity threats, heightened awareness is not enough. To truly capture their attention, it’s critical to deliver a compelling narrative about what the cybersecurity data you’re presenting actually means in terms of risk—to the hospital, to patients, and possibly even to them as the leadership.
Executive leadership thinks in terms of risk, making it essential to translate cybersecurity into “human risk” by telling the story behind the data.
Prioritize regular and relevant cybersecurity training
Cybersecurity training for employees isn’t a one-off task; it’s an ongoing commitment. While a brief session might satisfy HIPAA requirements, it doesn’t significantly diminish the risk of cyber or ransomware attacks.
The question then arises: How can security leaders design training that resonates with healthcare professionals and genuinely nurtures a proactive cybersecurity culture?
Here are some tips:
1. Set standards and uphold them
If your hospital has yet to define its stance on cybersecurity, the time to act is now. Without set standards, holding employees accountable becomes difficult. Thoughtfully crafted policies emphasize the importance of cybersecurity, allowing leadership to address non-compliance effectively.
A note of advice: You’ll be more impactful at consistently reducing risk within your organization if you take the approach of empowering users rather than making them feel punished. The focus should be on the lessons learned in the failure, not the mistake. That said, if an employee repeatedly makes mistakes, and the course is never corrected, then that needs to be addressed.
For example, an employee who consistently fails phishing tests without facing any corrective measures exposes the organization to a cyber attack. If that attack is successful, it could be argued that the hospital is failing to recognize and mitigate human risk.
While it’s unreasonable to penalize an employee based on a single misstep in a phishing exercise, repeated negligence, especially when it culminates in a real breach, demands serious discussions and potential repercussions. The key is to clearly define expected behaviors and consistently communicate them through regular training sessions.
2. Offer brief, engaging training content
Given union considerations, even an annual 15-minute cyber training might be a point of contention in some hospitals. Considering the extensive training healthcare professionals undergo for a variety of other areas, it’s a fair concern. However, when it comes to training and educating employees on cybersecurity, frequency and brevity are paramount.
Rather than enduring lengthy lectures on phishing or passphrases, employees can benefit from short, engaging training sessions. Presenting these as tools for personal data protection, as well as a benefit to the hospital and its patients, can often be more impactful.
Modern training approaches even feature five- to ten-minute Hollywood-caliber episodic productions designed to keep the user coming back on their own just to see what happens in the next episode. Along the way they learn valuable cybersecurity practices and tips.
It’s also helpful to supplement formal training with easily accessible resources such as break room posters, infographics, and electronic signage, catering to those who might not have time for regular sessions or who don’t regularly check their work email.
In short, the occasional, annual training session that merely serves to check a HIPAA compliance box is seldom effective. Real change and risk reduction demands more.
3. Tailor your cybersecurity training for healthcare
While the fundamentals of cybersecurity training remain consistent across industries, the delivery method should be tailored to the specific needs of the healthcare sector. The same password protocols apply whether you work in a bank, school, or hospital. However, how healthcare professionals access information is often unique.
For example, many don’t have dedicated computers, relying instead on Workstations on Wheels, which do not have speakers. In these situations, assigning video training without audio solutions won’t be effective. These unique challenges are important to recognize so that cybersecurity training accommodates those with technology limitations.
4. Be visible and available
As a hospital’s security leader, it’s easy to get consumed by reports, meetings, and IT crises that tend to confine you to your office or data center. However, it cannot be overstated how beneficial it is to allocate time for proactive “Security By Walking Around” (SBWA) assessments.
By positioning the security team as approachable allies, rather than enigmatic figures, staff will be more likely to bring potential security concerns to you, possibly flagging issues before they escalate into breaches.
Even though they may occasionally seek advice on personal cybersecurity matters, these interactions present valuable opportunities to reinforce security awareness. You might not have a solution for every problem, like a friend’s stolen identity, but you can offer insightful cybersecurity advice and a listening ear.
5. Phish every employee once a quarter (at least)
Sending phishing emails to employees at least once a quarter can be an insightful way to gauge the effectiveness of your cybersecurity training. Those who repeatedly fall for these tests might benefit from more frequent checks, possibly monthly. While a single failure can happen to anyone, consistent errors indicate a need for intensified training.
Organizing and executing multiple phishing tests can be daunting, but automation tools can simplify and manage the process efficiently.
Couple raising awareness with tighter IT security controls
In addition to continual employee education on phishing and cybersecurity, reducing the number of ways bad actors can infiltrate your IT infrastructure should also be explored. Here are three options to consider:
1. Invest in monitoring software
You can’t measure what you can’t monitor. In addition to phishing automation software, invest in software to monitor your network. You want a program that not only alerts staff to adverse events, but also provides context to the criticality of the event using an easy-to-read dashboard. Since systems need monitoring 24/7/365, some hospitals outsource this function to a managed security services provider (MSSP).
2. Lock down systems where possible
Do all employees need access to the hospital’s email system? Is it essential for claims specialists to access the EHR? Carefully review each software application to determine who really needs to use it.
Given that healthcare professionals often work extended 12-hour shifts and unconventional hours, it’s understandable they might wish to check their personal email, shop on Amazon, or browse social sites during breaks. However, for security and productivity reasons, consider establishing controls that restrict access to such sites on hospital devices.
Ensure that your policies are realistic and accommodate human behaviors. Clearly communicate to your staff that they are welcome to handle personal matters on their own devices, using the hospital’s guest network, during their designated breaks.
3. Use role-based access to software
In addition to limiting access to non-essential software, implement role-based permissions for software that employees genuinely require. For instance, while an administrative clerk might require basic access to the general ledger system, they likely don’t need privileges for consolidated financial reports or analytical tools. By customizing software access based on job title, department, and other relevant factors, hospital IT teams can minimize the network’s vulnerability to potential threats.
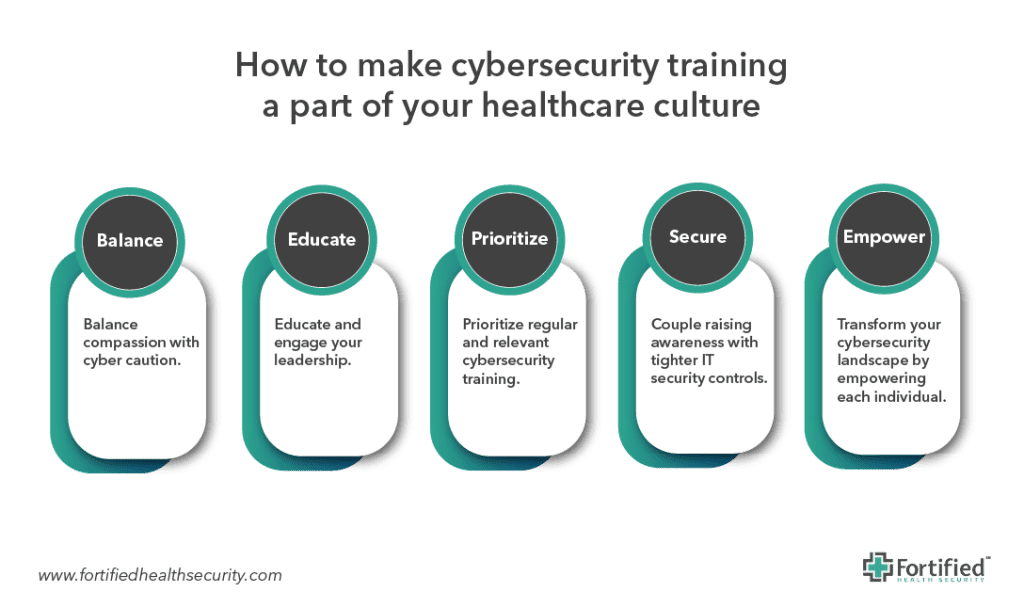
Human-Centered Cybersecurity
In an era where cyberattacks are perpetually on the rise, the healthcare sector stands at a particularly vulnerable juncture. The fusion of compassion and trust, which are the hallmarks of healthcare professionals, unintentionally presents an avenue for exploitation.
While technology evolves at an accelerated pace, the human element remains a constant – and it’s this human touch, so intrinsic to healthcare, that cybercriminals are targeting.
It is not merely about meeting regulatory standards or checklists; it’s about transforming the cybersecurity landscape by empowering each individual. This is not just a technical battle; it’s a cultural shift – one that demands consistent, engaging, and tailored training, combined with leadership commitment and regular testing.
By taking this holistic approach, we’re better able to protect patient data, preserve trust, and ensure that healthcare remains resilient against cyber threats.
For real-world advice on how to cultivate and maintain a strong, cyber aware culture within your healthcare organization, check out our on-demand webinar, The Art & Science Behind a Strong Cybersecurity Culture.


